The concept of “gamification” — incorporating fun, competitive games into everyday practices — has been adopted in diverse industries to shift human behavior. Wearable devices like FitBit use gamification to motivate people to outpace their friends in exercising. Investment apps like Robin Hood and Coinbase have built-in game-like features to encourage and reward trading (for better or worse).

With a grant from the Center for Long-Term Cybersecurity, a pair of researchers from the UC School of Berkeley’s Masters of Information and Cybersecurity (MICS) program completed a 2021 capstone project that sought to “gamify” one of the most important elements of digital security: choosing a strong password.
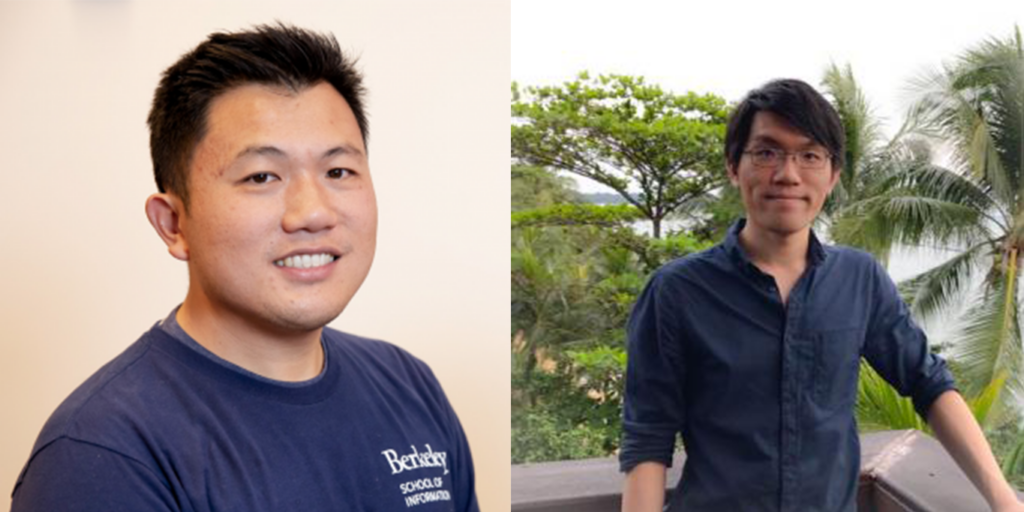
“We noticed the trend of gamification in different industries to attract younger generations, so our question was, can primary school children learn basic cybersecurity concepts through playing games?” explains David Ng, who carried out the project with fellow student, Jacky Ho. (Ng is Director of Product Management at Salesforce, focused on using data science for cybersecurity; Ho is based in Singapore, and is Director of Regulatory Advisory at UBS.)
“We wanted to do something that could impact society,” Ho says. “Classroom learning is pretty boring sometimes. Cybersecurity is often too hard to understand, and young people just want to have fun. When we talk about fun, we talk about games. So we thought, why don’t we make cybersecurity education a game?”
Ng and Ho knew they wanted to create a game for their project, but because neither of them is a game developer, they turned to a mini-game hosting platform called itch.io and organized a “Game Jam,” through which online developers were invited to submit games as part of a competition. The pair, along with other students, used funding from CLTC to offer financial prizes as an incentive to participate. They also created a Discord for developers from the community to ask questions and collaborate.

Participating developers were given the option to choose one of two themes for their game design: “Good Password and Bad Password,” to teach players how to compose a good password and avoid composing bad passwords, or “Endpoint/User Cybersecurity,” to teach players to identify potential phishing emails or other sources of ransomware and to secure their endpoint computers. All the games submitted were required to run on an HTML browser and have a total duration of less than 15 minutes. Developers were also advised not to include “NSFW” content or copyrighted assets.
After a two-week entry period, the pair’s Cybersecurity Game Jam received 43 entries, with submissions not just from the United States, but also from Germany, Turkey, Nepal, and other countries. The games had names like “You are the Firewall” and “Phish Bait,” and took a wide variety of approaches to teaching digital security basics. The game Officeware, for example, puts a clever spin on endpoint security: the player has to move around an office, updating software on different computers. “We wanted to use the power of the community,” Ng says. “One of the challenges we ran into was, how do we distribute the prize, since people are in different countries, and we wanted to protect their identities.”
A team of judges evaluated the games based on factors such as playability, design, and creativity, as well as appropriateness for different ages and effectiveness in teaching principles related to cybersecurity.
One of the top winners was a password mini game called “Cryptic Clash,” in which players create passwords that literally battle against other passwords, with their relative strength resulting from their length and complexity. “If you have a weaker password, you will lose the game,” Ho says. “If your password is stronger, you can pass to the next level.”

Ng and Ho tested the effectiveness of Cryptic Clash in teaching cybersecurity skills by enlisting two groups of children — between the ages of 6-12 and 12-18 — to provide feedback. “They really enjoyed the game,” Ng says. “They played it for about 10 minutes each, and just from a small sample size, they did create a more complex password after playing compared to a control group.”
Ng and Ho hope to continue the project and develop games related to other cybersecurity topics. “The next stage is trying to find opportunities to organize another game jam with other topics, like ransomware or data leakage,” Ho says. “As more and more people gain internet connectivity and have emails and passwords, cybersecurity incidents are going to happen exponentially more often than today. Password management is something that everybody needs to learn. It’s not just children, but adults also need to be more aware and cognizant of these threats.”
“We proved that we can crowdsource high-quality and innovative mini-games through the community with very few resources,” Ng says. “Part of CLTC’s mission is to bring more awareness to cybersecurity, and I think we achieved that.”
Watch a video below of Ng and Ho presenting their project at the 2021 CLTC Research Exchange.